- Template on the Certificate Server, refer to the Intune documentation. To create PKCS certificate profile: 1. In the Intune admin console, select the POLICY icon. Click Add Policy. In the Create a New Policy window, from Android (or iOS) list, select PKCS (.PFX) Certificate Profile and click Create Policy.
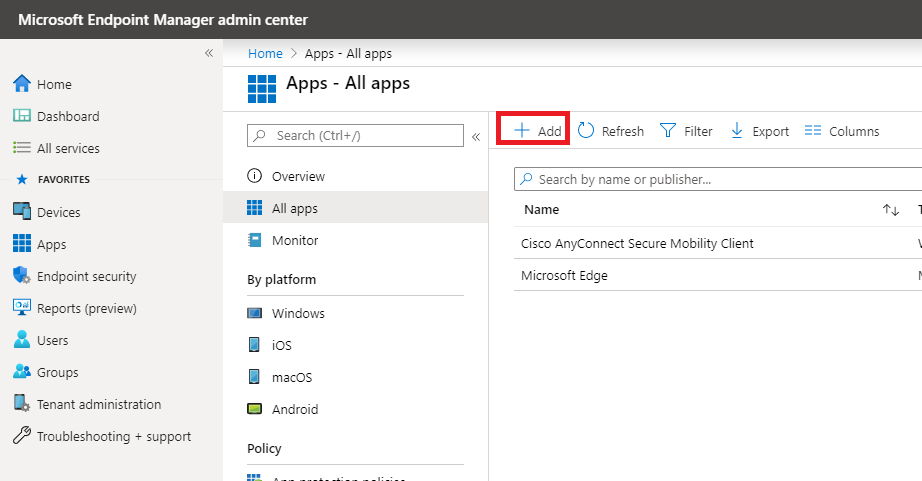
- Microsoft InTune Details For more information about using the Cisco Umbrella AnyConnect module with the InTune Mobile Device Manager, see InTune documentation, available online at Microsoft's docs website. Publish the Umbrella AnyConnect app to managed Android devices In your InTune dashboard, navigate to Apps All Apps Add Application.
 -->
-->Intune pushes all the profiles to the device (iPhone in this case). When I open up Anyconnect (non-legacy) it sees the profile, when I try to connect it comes up with the following: This connection requires a client certificate, but no matching certificate is configured. Plerase modify the connection, choose a valid certificate, and try again. It has taken a long time, and there have been plenty of bumps along the way, but it’s finally available in public preview: You can perform a user-driven Hybrid Azure AD Join deployment over the internet, using a VPN connection to establish connectivity so the user can sign into the device.
Intune integrates with network access control (NAC) partners to help organizations secure corporate data when devices try to access on-premises resources.
Important
NAC is not currently supported for Android Enterprise Fully Managed or Android Enterprise Dedicated devices.
How do Intune and NAC solutions help protect your organization resources?
NAC solutions check the device enrollment and compliance state with Intune to make access control decisions. If the device isn't enrolled, or is enrolled and not compliant with Intune device compliance policies, then the device should be redirected to Intune for enrollment, or for a device compliance check.
Example
If the device is enrolled and compliant with Intune, the NAC solution should allow the device access to corporate resources. For example, users can be allowed or denied access when trying to access corporate Wi-Fi or VPN resources.
Feature behaviors
Devices that are actively syncing to Intune can't move from Compliant / Noncompliant to Not Synched (or Unknown). The Unknown state is reserved for newly enrolled devices that haven't been evaluated for compliance yet.
For devices that are blocked from access to resources, the blocking service should redirect all users to the management portal to determine why the device is blocked. If the users visit this page, their devices are synchronously reevaluated for compliance.
NAC and Conditional Access
NAC works with Conditional Access to provide access control decisions. For more information, see Common ways to use Conditional Access with Intune.
How the NAC integration works
The following list is an overview on how NAC integration works when integrated with Intune. The first three steps, 1-3, explain the onboarding process. Once the NAC solution is integrated with Intune, steps 4-9 describe the ongoing operation.
Intune Cisco Anyconnect Download
- Register the NAC partner solution with Azure Active Directory (AAD), and grant delegated permissions to the Intune NAC API.
- Configure the NAC partner solution with the appropriate settings including the Intune discovery URL.
- Configure the NAC partner solution for certificate authentication.
- User connects to corporate Wi-Fi access point or makes a VPN connection request.
- NAC partner solution forwards the device information to Intune, and asks Intune about the device enrollment and compliance state.
- If the device isn't compliant or isn't enrolled, the NAC partner solution instructs the user to enroll or fix the device compliance.
- The device tries to reverify its compliance and enrollment state when applicable.
- Once the device is enrolled and compliant, NAC partner solution gets the state from Intune.
- Connection is successfully established which allows the device access to corporate resources.
Use NAC for VPN on your iOS/iPadOS devices


NAC is available on the following VPNs without enabling NAC in the VPN profile:
- NAC for Cisco Legacy AnyConnect
- F5 Access Legacy
- Citrix VPN
NAC is also supported for Cisco AnyConnect, Citrix SSO, and F5 Access.
To enable NAC for Cisco AnyConnect for iOS
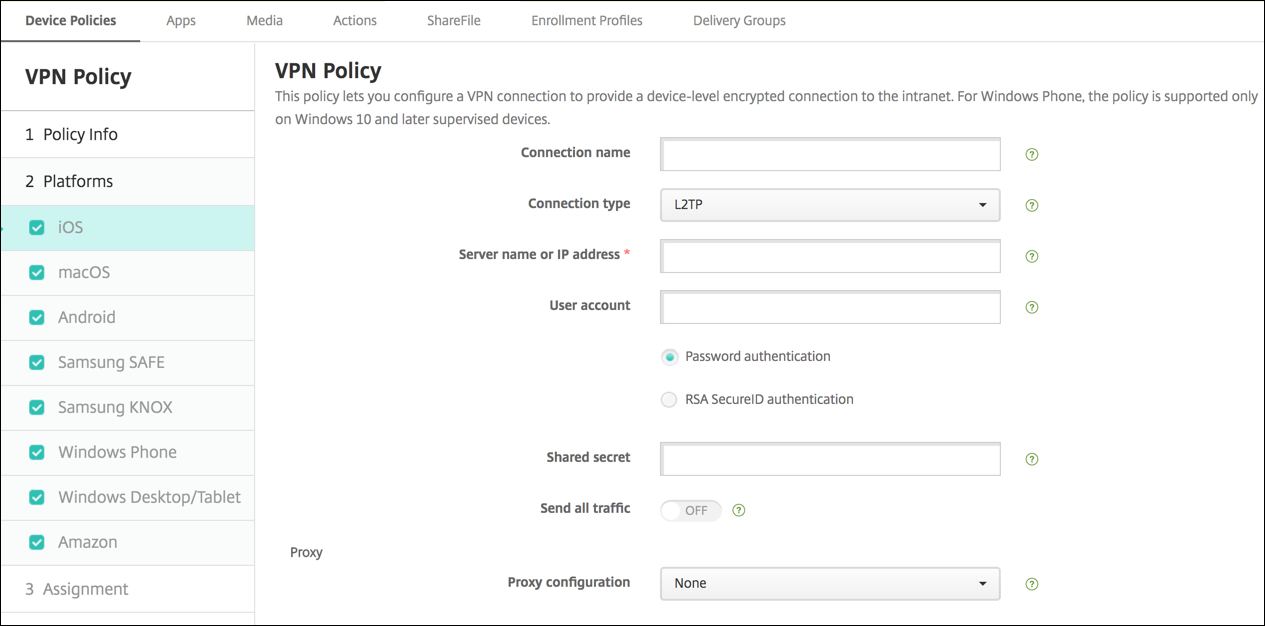
Intune Cisco Anyconnect Vpn Profile
- Integrate ISE with Intune for NAC as described in the link below.
- Set the Enable Network Access Control (NAC) setting in the VPN profile to Yes.
To enable NAC for Citrix SSO
- Use Citrix Gateway 12.0.59 or higher.
- Users must have Citrix SSO 1.1.6 or later installed.
- Integrate NetScaler with Intune for NAC as described in the Citrix product documentation.
- In the VPN profile, select Base settings > Enable Network Access Control (NAC) > select I agree.
Intune Cisco Anyconnect
To enable NAC for F5 Access
Cisco Anyconnect Intune Macos
- Use F5 BIG-IP 13.1.1.5 or later.
- Integrate BIG-IP with Intune for NAC. The Overview: Configuring APM for device posture checks with endpoint management systems F5 guide lists the steps.
- In the VPN profile, select Base settings > Enable Network Access Control (NAC) > select I agree.
The VPN connection is disconnected every 24 hours for security reasons. The VPN can immediately be reconnected.
We're working with our partners to release a NAC solution for these newer clients. When solutions are ready, this article will be updated with additional information.
Next steps




